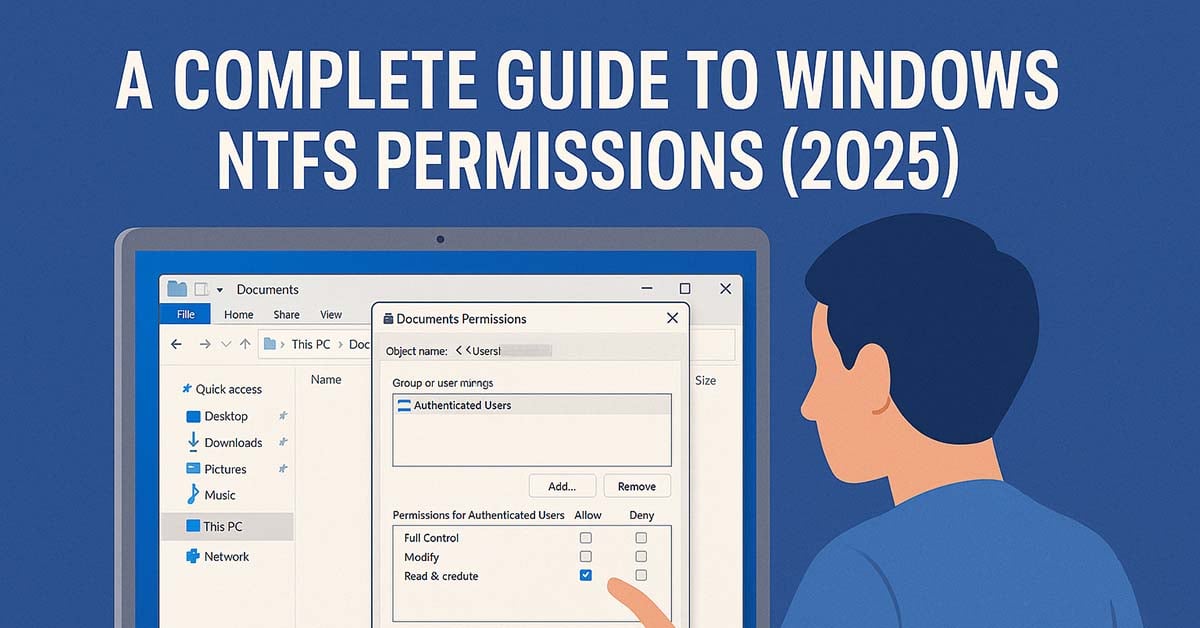
A Complete Guide to Windows NTFS Permissions
In Windows, permissions are available on every file, folder, registry key, printer and Active Directory object. However, in this article we’ll be concentrating on NTFS file and folder permissions. These permissions are available on NTFS file systems but not on FAT based file systems.
Permissions define what a user can and cannot do with a file or folder. For example, they may be used to allow some users to read a file and disallow others from reading it. They could also be used to stop some users deleting or modifying files etc.
Table of Contents
Basic NTFS Permissions
There are basic and advanced permissions (see below).
The basic permissions map to one or more advanced permissions. For example, if you set the basic Read permission on a file then it means you have the following advanced permissions: List Folder/Read Data, Read Attributes, Read Extended Attributes and Read Permissions. Basic permissions provide a simpler and less granular way to set permissions. Another way to think of it is that basic permissions are groups of advanced permissions.
The basic permissions are:
| Permission | What It Allows |
|---|---|
| Full Control | Read, modify, add, move, and delete files and directories. Users can also change permissions and take ownership. |
| Modify | View and modify files, including adding, deleting, and changing file properties. |
| Read & Execute | View files and run executable files, including scripts or programs. |
| Read | View files and their properties, but cannot modify them. |
| Write | Write to files, add new files to directories, but cannot delete existing files unless Modify or higher is granted. |
Basic vs. Advanced NTFS Permissions
NTFS permissions come in two forms: basic permissions and advanced permissions. Understanding the difference is critical for applying secure file permissions and simplifying management.
| Feature | Basic Permissions | Advanced Permissions |
|---|---|---|
| Level of Detail | Grouped, easy-to-apply settings | Granular, fine-tuned control options |
| Examples | Full Control, Modify, Read & Execute, Read, Write | Traverse Folder, List Folder, Read Attributes, Write Data, Delete, Change Permissions, Take Ownership, etc. |
| Typical Use | General access control for most users | Specific security configurations, especially for sensitive data |
| Management Complexity | Simpler for IT teams to apply quickly | Requires detailed understanding of NTFS security |
In practice, basic permissions are often sufficient for everyday file and folder access. Use advanced permissions when you need precise control over what users can do at a more technical level.
Advanced NTFS Permissions
The advanced permissions are:
Traverse Folder/Execute File: For folders: Traverse Folder allows or denies moving through folders to reach other files or folders, even if the user has no permissions for the traversed folders. (Applies to folders only.)
Traverse folder takes effect only when the group or user is not granted the Bypass traverse checking user right in the Group Policy snap-in. (By default, the Everyone group is given the Bypass traverse checking user right.) For files: Execute
File allows or denies running program files. (Applies to files only). Setting the Traverse Folder permission on a folder does not automatically set the Execute File permission on all files within that folder.
List Folder/Read Data: List Folder allows or denies viewing file names and subfolder names within the folder. List Folder only affects the contents of that folder and does not affect whether the folder you are setting the
permission on will be listed. (Applies to folders only.) Read Data allows or denies viewing data in files. (Applies to files only.)
Read Attributes: Allows or denies viewing the attributes of a file or folder, such as read-only and hidden. Attributes are defined by NTFS.
Read Extended Attributes: Allows or denies viewing the extended attributes of a file or folder. Extended attributes are defined by programs and may vary by program.
Create Files/Write Data: Create Files allows or denies creating files within the folder. (Applies to folders only). Write Data allows or denies making changes to the file and overwriting existing content. (Applies to files
only.)
Create Folders/Append Data: Create Folders allows or denies creating folders within the folder. (Applies to folders only.) Append Data allows or denies making changes to the end of the file but not changing, deleting, or overwriting
existing data. (Applies to files only.)
Write Attributes: Allows or denies changing the attributes of a file or folder, such as read-only or hidden. Attributes are defined by NTFS. The Write Attributes permission does not imply creating or deleting files or folders,
it only includes the permission to make changes to the attributes of a file or folder.
Write Extended Attributes: Allows or denies changing the extended attributes of a file or folder. Extended attributes are defined by programs and may vary by program. The Write Extended Attributes permission does not imply
creating or deleting files or folders, it only includes the permission to make changes to the extended attributes of a file or folder.
Delete Subfolders and Files: Allows or denies deleting subfolders and files, even if the Delete permission has not been granted on the subfolder or file. (Applies to folders.)
Delete: Allows or denies deleting the file or folder. If you do not have Delete permission on a file or folder, you can still delete it if you have been granted Delete Subfolders and Files on the parent folder.
Read Permissions: Allows or denies reading permissions of the file or folder, such as Full Control, Read, and Write.
Change Permissions: Allows or denies changing permissions of the file or folder, such as Full Control, Read, and Write.
Take Ownership: Allows or denies taking ownership of the file or folder. The owner of a file or folder can always change permissions on it, regardless of any existing permissions that protect the file or folder.
Assigning, Allowing and Denying NTFS Permissions
Permissions are assigned explicitly or by inheritance. For example, a file could inherit its permissions from its parent folder. This makes managing permissions simpler as you only need to change one folder’s permission instead of all the files in a folder. You can also set explicit permissions for a file or a folder. For example, a file could still inherit its permissions from its parent folder but you may also want to give extra permissions to a specific user.
You can allow or deny a permission. Deny beats Allow if they are applied on the same file or folder. If the permissions are inherited, then the Allow and Deny work a bit differently. It is based on a hierarchy:
- Explicit Deny
- Explicit Allow
- Inherited Deny
- Inherited Allow
These are checked, by Windows, from first to last, and once one is matched then that security is used. For example, if the inherited permissions on a file are that you are denied read permission, but you are explicitly given read permission on the file, then that explicit permission overrides the inherited deny permission.
The security applies to both users and groups. Users can be members of one or more groups. For example, you could have a group for accountants, editors, programmers, etc. You can then base your permissions on groups instead of specific users. This makes managing the permissions much simpler as a new employee can simply be added to the appropriate groups. They can then access files and folders based on their group and no permissions need to be changed.
Files and folders have ownership. When a file or folder is created Windows gives Full Control to the owner (the creator of the file or folder). You can change ownership, but the user or group changing the ownership needs the Full Control or Take Ownership permission.
How to Grant Full NTFS Permissions in Windows 10/11
When managing Windows file and folder permissions, there will be times when you need to allow a user (probably yourself) Full Control. This will provide a user with read, write, modify, delete, and take ownership access to a file or folder. Giving full control of Windows permissions is simple, but care needs to be taken so that access is not accidental.
Steps to Grant Full Control NTFS Permissions:
- Open Windows Explorer and navigate to the correct drive, network location, etc.
- Right-click the file or folder that you want to manage, and then click Properties.
- Go to the Security tab and click Edit.
- In the Permissions for [file/folder] dialog box, click the Add button, type the name of the user or group, and click Check Names to verify.
- After adding the user, select them from the list and check the Full Control box beneath the Allow column.
- Click Apply, then OK to save the changes.
You may need administrative credentials for system-wide folders or shared network paths. It's best practice to audit changes with Advanced Security Settings in order to view permission inheritance and effective access.
Key Considerations:
- Granting Full Control gives complete access to the file or folder, including the ability to delete it or change permissions.
- Use this setting only when necessary, especially in shared or multi-user environments.
- For more secure configurations, consider assigning only the minimum required permissions (e.g., Modify or Read & Execute).
NTFS Permissions Best Practices for Secure File Access
To maintain a strong NTFS security policy and ensure secure file permissions, follow these essential best practices:
Use Groups, Not Individuals
Always assign permissions to security groups instead of individual user accounts. For example, create a group like Accounting-Staff and grant that group the required permissions on folders or files. This simplifies administration because when employees change roles, you only need to update their group membership. You avoid the time-consuming process of editing permissions for each file or folder individually, which also reduces the risk of oversight or inconsistent access.
Adhere to the Principle of Least Privilege
Grant users only the minimum permissions necessary to perform their job. This is known as the Principle of Least Privilege. For most users, the Modify permission provides sufficient access to read, edit, and delete files without giving control over permissions. Reserve Full Control for administrators, as it allows users to change security settings, take ownership, or delete critical files, increasing the risk of accidental or unauthorized changes.
Keep the Folder Structure Clean
Only IT administrators should create top-level folders. A clean and consistent folder structure makes managing permissions and inheritance straightforward. Allowing users to create folders at the root level can quickly lead to disorganization, complicating permission audits and increasing the risk of access mistakes.
Avoid Breaking Inheritance
Breaking permission inheritance deep within a folder structure adds complexity and increases the chance of security gaps. Instead of applying custom permissions far down the folder tree, consider restructuring your folders so permissions naturally flow through inheritance. This simplifies your NTFS permissions best practices strategy and makes troubleshooting much easier.
Conduct Regular Audits
Schedule quarterly or yearly audits of your NTFS permissions. These audits help you identify and remove unnecessary access, especially for former employees or users who have changed roles. Regular reviews are a critical part of maintaining secure file permissions and preventing unauthorized access to sensitive data.
Troubleshooting Common NTFS Issues
Even with the right NTFS permissions configured, you may encounter unexpected problems. Below are some common issues and how to resolve them:
Access Denied Despite Correct Permissions
One of the most frequent complaints is access denied errors, even when permissions appear correct. This often happens due to:
- A conflict with Share permissions. Both NTFS and Share permissions apply on network shares, and the most restrictive set applies.
- An explicit Deny permission overriding an Allow permission. Deny always takes precedence, so check group memberships carefully.
To identify the root cause, use the Effective Access tab within the Advanced Security Settings. This tool shows what permissions a specific user has, considering group membership, inheritance, and any deny rules.
Permission Changes Don’t Apply to Subfolders
If you’ve modified permissions but the changes aren’t propagating to subfolders or files, inheritance is likely broken. To correct this:
- Right-click the parent folder and select Properties.
- Go to the Security tab and click Advanced.
- Check the box labeled Replace all child object permissions with inheritable permissions from this object.
- Click Apply to enforce consistent permissions down the folder tree.
How to Reset NTFS Permissions to Default
If permissions are severely misconfigured or inconsistent, you can reset them using the command line. This restores default permissions recursively:
icacls "C:\path\to\folder" /reset /TThis command replaces all permissions on the target folder and its contents with default values, helping resolve stubborn NTFS permissions not applying issues.
NTFS vs. Share Permissions
When configuring file access in Windows, understanding NTFS vs Share permissions is essential for building a secure and manageable environment. Both types of permissions work together, but they operate differently:
| Feature | NTFS Permissions | Share Permissions |
|---|---|---|
| Where They Apply | Local access and network access | Network access only |
| Level of Control | Highly granular (Read, Modify, Full Control, etc.) | Basic options (Read, Change, Full Control) |
| Best Used For | Detailed security at the file and folder level | Limiting broad access to network shares |
The Golden Rule: The Most Restrictive Permission Applies
Whenever both NTFS and Share permissions are in place, the most restrictive permission applies. For example:
- NTFS Permissions: Modify
- Share Permissions: Read
In this case, when a user connects over the network, they will only have Read access, even though NTFS permissions allow more. Always consider both sets of permissions to avoid unexpected access limitations.
Microsoft-Recommended Best Practice
To simplify management and ensure consistent security, Microsoft recommends setting the Share Permission for Everyone to Full Control. You then use granular NTFS permissions to enforce access control. This approach centralizes your security model and avoids confusion between NTFS and Share permissions.